Obsolescence of Software
Piracy Potential
Through
Superior Architecture
Computer Architecture
CS3383
David B. Robert
6 April 2000
Table
Of Contents
Obsolescence of Software Piracy Potential Through Superior Architecture
Introduction
__________________________________________________________ 3
The Status Quo Regarding Software Piracy and the Missing Link______________
3
The Software and Hardware Relationship__________________________________
4
The Need For Protection_________________________________________________
5
Existing And
Tried Protective Methods____________________________________ 8
Software
Keys___________________________________________________ 9
Hardware Locks_________________________________________________
9
Copy Protection_________________________________________________10
The End User License Agreement
(EULA)___________________________12
A Workable Solution Through Superior Architecture _______________________ 15
Inventory Service_______________________________________________
18
Chip Size______________________________________________________
18
Internet Security with Positive User Identification
When Necessary_____ 19
Transition
Mechanism from CISC TO RISC________________________ 19
Piracy Deterrent Bar Implementation______________________________ 21
Conclusion___________________________________________________________
21
Bibliography_________________________________________________________
23
Obsolescence of Software Piracy Potential Through
Superior Architecture
Software piracy is a substantial problem that affects all of
us whether we know it or not. This paper will explore the current state of software piracy prevention along with methods that have been tried and failed in the past. A method that is recognized by the Computer Desktop Encyclopedia as the only copy protection method that works will be reviewed along with why this method is not universally accepted and used. Finally, an architectural solution that cannot only solve the software piracy dilemma, but also has the capability of bridging the CISC/RISC architectural gap while simultaneously providing a mechanism for increased Internet security will be presented. We are at the dawn of a new century and a new millennium; it is time to make software piracy a problem of the past. To present and generate interest in a method that can realize this possibility is the reason for this paper.
The
Status Quo Regarding Software Piracy and the Missing Link
The Business Software Alliance is the
preeminent advocate against software piracy for software publishers worldwide.
A visit to their Internet site at: 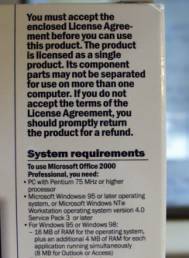 http://www.bsa.org/
reveals a wealth of information concerning software piracy. This statistic, “Worldwide
Software Piracy Losses Estimated At Nearly $11 Billion In 1998: Study Finds
More Than One-Third of Applications Are Pirate Copies”[BSAa] reveals
the current extent of the software piracy problem.
http://www.bsa.org/
reveals a wealth of information concerning software piracy. This statistic, “Worldwide
Software Piracy Losses Estimated At Nearly $11 Billion In 1998: Study Finds
More Than One-Third of Applications Are Pirate Copies”[BSAa] reveals
the current extent of the software piracy problem.
This photo shows two ubiquitous parts of practically every software purchase. The End User License Agreement or EULA has evolved into the predominant means of protection against software piracy, while the System requirements reveal the necessary operating system and hardware components the software needs to function properly. As computers have increased in complexity and efficiency the system requirements list has typically grown in size, but what is missing from this list? Under copy protection in The Computer Desktop Encyclopedia by Alan Freedman the reader is told that, “ SORRY, PERMISSION TO USE THIS QUOTE ON THE WEB WAS DENIED see sentence number one of the final paragraph for copy protection on page 179 ”[Freedman 99a] This system should be boldly announced on every system requirements list, yet it is sadly missing. The current extent of the software piracy problem hints at the impotence of the EULA. The advancements made by hardware over the years is truly remarkable, however the system requirements list has failed to produce a single component dedicated solely to the prevention of software piracy.
The Software and Hardware Relationship
“The one who controls the software controls the war.” -Katsuhide Hirai, Fujitsu Ltd., Quoted in Northeast International Business (November 1989)[Clapes93a]
~~~
Hardware and software complement each other. One without the other is worthless. Hardware provides the necessary platform for software to be able to do its magic. But, software provides the raison d'être for hardware. It is software that animates hardware and makes it useful and fascinating. Without meaningful software to imbue hardware with life a computer is about as useful as a pair of eyeglasses without lenses. While neither can meaningfully exist without the other, software’s reason for being is not the computer. Software exists for a myriad of purposes of which none are solely for the purpose of propping up hardware. Software has propelled hardware through its successes in the marketplace. Software availability has determined the success or failure of certain makes of computers. Yet as crucial as software is to the very existence of hardware, software has an intrinsic weakness that hardware has failed to protect. Clapes in Softwars puts it like this, “Computer programs suffer from an essential vulnerability: they are easy to copy. In contradistinction to the case of hardware products, copying of computer programs requires no research laboratories, no factories, no chemical formulas, and no strategic materials. Copying a computer program is no more difficult than duping an audiotape or plagiarizing a story. What can be freely copied cannot form the basis of a business if the copying can be done with impunity. Thus, the nature and extent of society’s rules against such copying actually dictate the boundaries of the software business. Further, because buyers of computers make their hardware purchases in large measure because of the software available for such computers, the rules against copying of software strongly influence competition for computer hardware. Hirai-san was right: the one who controls the software controls the war.” [Clapes93b]
Software piracy is a problem of monumental proportions. The spectrum of piracy covers a broad band. Anyone who has anything to do with computers has undoubtedly been offered illegitimate copies of some software product by someone thinking they are rendering a favor instead of committing a crime. Companies should be concerned with and have policies against employees loading unauthorized copies of software onto the company computers. "Companies are responsible for any unlicensed software that resides on their office computers It's therefore essential that businesses commit the time and money to educate employees about the importance of abiding by the company's software usage policy. Bottom line, it costs less to educate employees about the risks of copyright infringement than settling a software piracy claim with BSA," said Bob Kruger, vice president of enforcement for BSA. [BSAb] An employer may instruct an employee load up a pirated copy of some software and when the crucial moment comes to click “I Accept” the employee may wonder who is really responsible. When was the last time you read a EULA in its entirety before clicking “I Accept”? A search of the keyword, “piracy” in Microsoft’s help feature produces an assortment of topics; “Are there different types of software piracy? Is one type of piracy less damaging than any other? , What is software piracy? Why should I be concerned about it? , What should I do if I suspect I have unknowingly purchased illegal Microsoft software products?” Microsoft even includes a piracy hotline phone number: “Microsoft Piracy Hotline at 1-800-RU-LEGIT”; illustrating the corporate concern over this problem. Large scale pirate operations often operate in the open overseas where much of the loss occurs.[Record(Bergen County)]. Software piracy is as common as speeding, and is regarded with the same degree of seriousness by the average person.
The attitude of many is apathetic toward software piracy. Richard Baker in “Scuttle the Computer Pirates” writes that, “in some circles it’s considered fashionable, not dishonest, to copy programs and to give or sell them to your friends.” When piracy is brought up as an item of conversation it is relatively easy to find these views expressed. Baker concludes his social factors by pointing out that “all the effort you expend to obtain copyrights and other protection, and the precise legal language of a license agreement aren’t worth a public domain utility program when it comes to stopping a nation full of individual pirates who feel fully justified in what they do, and who are hard to catch in any event.” [Baker85] Baker’s comment suggests just how ineffective the legal means of protection are in preventing software piracy. Yet, the legal means of prevention has gained the dominant position as a method of choice for protection. Books have been written covering every aspect of legal protection. Up to now, hardware, in spite of all of its grandiose ingenuity has failed to provide a universally acceptable means of piracy prevention. Davis in Software Protection points out that, “all existing schemes have significant drawbacks to universal use in place of legal remedies. Until an infallible technical solution is devised, the software industry will have to rely on legal remedies, and suffer from the imperfections of an imperfect legal system devised for imperfect humans.” [Davis85a]
An infallible technical solution for piracy prevention has long been sought after since the early days of software existence, however finding something successful has been as illusive as the quest for the Holy Grail. A search of The IBM Patent Database Server at http://www.patents.ibm.com/ for software protection devices yields a myriad of technical solutions for piracy prevention, yet very few of these devises have seen the light of day. Technology thresholds, ill devised schemes that bred bad will among end users, failure of the computing community to collectively support a method of merit have all contributed to the lack of a universally accepted system to protect the lifeblood of the computing industry.
The progression of hardware from its beginning through the 8088 machines to the current day marvels has been and will continue to be remarkable and life changing.
“SORRY PERMISSION DENIED TO USE THE TWO LOWER PICTURES ON PAGE 167 AND THE INSTALLATION QUOTE ON SAME PAGE OF THE COMPUTER DESKTOP ENCYCLOPEDIA” [Freedman99b]
Many peripheral devices have been and are invented to supplement the computer. The monitor, the keyboard, a mouse, speakers, floppy drives and now CD-Rom drives are visible components whose importance and usefulness are readily understood by the casual user. Data buses, caches, the CPU, translation lookaside buffers, and many other esoteric components makeup the mysterious black magic of the inner workings of the computer. All of these components work together through binary arithmetic to give the computer its remarkable ability. They attest to the capabilities of the design experts. Yet, the total architecture of the machine has failed miserably to produce a ubiquitous device with the acceptability of a CD-Rom drive to safeguard the producers of software and the legitimate users of software who are reduced to clicking “I Accept” if they want to experience the magic that brings a computer to life and makes it meaningful. The need for a technologically superior method of protection is crucial to making the software piracy problem a thing of the past.
Existing And Tried Protective Methods
Although it is deplorable that no such protective means has arisen to prominence, the industry cannot be blamed for not trying. Too many methods to fully discuss have been tried. Some have had limited success while others have fallen on the trash heap of consumer rejection. Davis in Software Protection: Practical and Legal Steps to Protect and Market Computer Programs says it like this, “Let’s examine, briefly, what technological means may be available in software or hardware to physically protect the software from being copied illegally. Most such attempts have been technologically unsuccessful for a variety of reasons, and most consumers appear to resist them, aggressively. Such devices must either be in or connected to the hardware, or be an integral element of the software.” [Davis85b]
Software keys appeared on the scene for a short period of time. A specific disk called the key was required to be inserted into the computer anytime the user wanted to use a particular program. If the disk was misplaced, lost, or destroyed the user was simply out of luck. The added hassle of keeping track of these disks did not sit well with many users who want the convenience to sit and go immediately into a project rather than hunt and search for the necessary disk key. Convenience rates high marks when it comes to computing and software keys failed to deliver.
Hardware keys or locks also known as dongles improved upon the software keys. Hardware locks are still in use today. Rainbow Technologies Inc. is one such company that provides these devises and has been in existence for approximately fourteen years. Hardware locks generally connect to the computers parallel port. The protected software looks for the lock. If it is present the user is able to conveniently utilize the software with out any concern to find something to stick into the computer to make the software work. The hardware lock is basically transparent. Once it is stuck in place, the user no longer has to worry about it. With Hardware locks the user is free to sit and go immediately into his desired project without the concerns of the software key. Hardware locks are usually found with high priced software such as Intergraph’s MicroStation, and Autodesk’s, Autocad. Mark Straley with Rainbow Technologies Inc. said that programs generally need to retail for around $500.00 before a producer of software should consider a hardware lock as a feasible means of protection. Straley said this threshold might eventually be lowered.[Straley] However, if every thirty-dollar program could utilize a hardware lock, how would the user manage to hook them all to a single parallel port? One or two jutting out of the backside of a computer usually present no problems, but a dozen or more of these devices sticking out the back would certainly be unwieldy. Hardware locks have also been cracked in the past, however Straley said since the Sentinial Super Pro they have not been cracked. If only they were more readily affordable with a compact means of stacking them, this is proven technology that has and does work. It is interesting to note that Freedman in The Computer Desktop Encyclopedia states, “SORRY PERMISSION DENIED TO USE QUOTE FROM COPY PROTECTION IN THE COMPUTER DESKTOP ENCYCLOPEDIA”[Freedman 99c]
Copy protection can be considered as a legal means such as copyrights and patents or a mechanical means such as methods that prevent the duplication of disks. Freedman puts it like this, “SORRY PERMISSION DENIED TO USE QUOTE ON THE WEB”[Freedman 99d] Rather than preventing unauthorized copying of software, a hardware lock actually prevents the unauthorized use of software. A user can make as many copies as he wants, but only the copy connected to the hardware lock will be fully functional. The mechanical means have largely been rejected because a user often has legitimate needs requiring the copying of some software. The legal means of protection, despite its inefficacy, has eclipsed all other methods of piracy prevention. The EULA or end user license agreement is now a main part of practically every software sale. These complicated legal documents have evolved with increasing complexity from their beginnings. It was common to find the term, “like a book” in the early simpler agreements. The agreements stated software was meant to be utilized like a book. A book cannot be in two places at the same time. The like a book theory is nice in context, however the mentioned ease of duplicating software leaves it in reality nothing like a book. You may use a copy machine to duplicate a book you want to share with another, but it takes a considerable amount of time to run off a copy of each page. After the copy is made, it is considerably substandard compared to the original. Whereas it is quite easy to make a copy or several copies of some software and the copied product’s quality is the same as the original minus good technical support and good documentation. A book has practical implications that prevent it from being commonly copied, while software does not. So while “like a book” was a nice analogy, it did not fit the situation like a glove.
Mechanical copy protection has strived to make software truly like a book, however mechanical methods have largely failed. With the right technological solution, software has the potential of being better than a book. Hardware locks permit software to function only as a demo version, if the key is absent. A demo can be freely passed around permitting a user to savor the qualities of the software while not being able to utilize its full potential. This enables the user to make an informed choice in his purchase decision, and prevents a user from buying a completely untried product only to have his expectations shattered once it is installed. If a user has tried a demo and then buys the full course it is unlikely that he or she will be dissatisfied.
The End
User License Agreement (EULA)
The EULA or end user
license agreement has become a major part of every software purchase. A notice stating that “you must
accept the enclosed License Agreement” before you can use the product can
be found near the system requirements list on many software packages. A typical installation generally displays a
copy of the EULA and a message box with the now ubiquitous “I accept” button
pops up for the installer to click.
Failure to click the “I accept” button negates the installation
and leaves the particular software unusable on the computer in question. It is strongly recommended that the
installer read and understand the EULA prior to acceptance, however there is no
means to indicate that you did read and do understand the EULA prior to
clicking the “I accept” button.
Also, there is no way of knowing if the responsible party clicked the
button or the boss simply had a subordinate do the dirty deed. The EULA is a legal and binding document, and
clicking the “I accept” button is considered the same as signing your
name to a legal document. A typical
EULA is shown in its entirety below.
Note the admonition to READ CAREFULLY on the first line.
END-USER LICENSE AGREEMENT FOR MICROSOFT
SOFTWARE IMPORTANT - READ CAREFULLY: This Microsoft End-User
License Agreement ("EULA") is a
legal agreement between you (either an individual or a single entity) and
Microsoft Corporation for the Microsoft software product identified above,
which includes computer software and may include associated media, printed
materials, and "online" or electronic documentation ("SOFTWARE
PRODUCT"). The SOFTWARE PRODUCT also includes any
updates and supplements to the original
SOFTWARE PRODUCT provided to you by Microsoft. Any software provided along with
the SOFTWARE PRODUCT that is associated with a separate end-user license
agreement is licensed to you under the terms of that license agreement. By
installing, copying, downloading, accessing, or otherwise using the SOFTWARE PRODUCT,
you agree to be
bound by the terms of this EULA. If you do not
agree to the terms of this EULA, do not install or use the SOFTWARE PRODUCT;
you may, however, return it to your place of purchase for a full refund.
SOFTWARE PRODUCT LICENSE
The SOFTWARE PRODUCT is protected by copyright
laws and international copyright treaties, as well as other intellectual
property laws and treaties. The SOFTWARE PRODUCT is licensed, not sold.
1. GRANT OF LICENSE. This EULA grants you the
following rights:
* Applications Software. You may install, use,
access, display, run, or otherwise
interact with ("RUN") one copy of the SOFTWARE PRODUCT, or any prior
version for the same operating system, on a single computer, workstation,
terminal, handheld PC, pager, "smart phone," or other digital
electronic device ("COMPUTER"). The primary user of the COMPUTER on
which the SOFTWARE
PRODUCT is installed may make a second copy
for his or her exclusive use on a portable computer.
* Storage/Network Use. You may also store or install
a copy of the SOFTWARE PRODUCT on a storage device, such as a network server,
used only to RUN the SOFTWARE PRODUCT on your other COMPUTERS over an internal
network; however, you must acquire and dedicate a license for each separate
COMPUTER on which the SOFTWARE PRODUCT is RUN from the storage device. A
license for the SOFTWARE PRODUCT may not be shared or used concurrently on
different COMPUTERS.
* License Pack. If this package is a Microsoft
License Pack, you may RUN additional copies of the computer software portion of
the SOFTWARE PRODUCT up to the number of copies specified above as
"Licensed Copies." You are also entitled to make a corresponding
number of secondary copies for portable computer use as specified above.
* Reservation of Rights. All rights not
expressly granted are reserved by Microsoft.
2. DESCRIPTION OF OTHER RIGHTS AND
LIMITATIONS.
* Academic Edition Software. If the SOFTWARE
PRODUCT is identified as "Academic Edition" or "AE," you
must be a
"Qualified Educational User" to use
the SOFTWARE PRODUCT. If you are not a Qualified Educational User, you have no
rights under this EULA. To determine whether you are a Qualified Educational
User, please contact the Microsoft Sales Information Center/One Microsoft
Way/Redmond, WA 98052-6399 or the Microsoft subsidiary serving your country.
* Not for Resale Software. If the SOFTWARE
PRODUCT is labeled "Not For Resale" or "NFR," then,
notwithstanding other sections of this EULA, your use of the SOFTWARE PRODUCT
is limited to use for demonstration, test, or evaluation purposes and you may
not resell, or otherwise transfer for value, the SOFTWARE PRODUCT.
* Limitations on Reverse Engineering,
Decompilation, and Disassembly. You may not reverse engineer, decompile, or disassemble
the SOFTWARE PRODUCT, except and only to the extent that such activity is
expressly permitted by applicable law notwithstanding this limitation.
* Separation of Components. The SOFTWARE
PRODUCT is licensed as a single product. Its component parts may not be
separated for use on more than one COMPUTER.
* Trademarks. This EULA does not grant you any
rights in connection with any trademarks or service marks of Microsoft.
* Rental. You may not rent, lease, or lend the
SOFTWARE PRODUCT.
* Application Sharing. The SOFTWARE PRODUCT
may contain Microsoft NetMeeting, a product that enables applications to be
shared between two or more COMPUTERS, even if an application is installed on
only one of the COMPUTERS. You may use this technology with all Microsoft
application products for multiparty conferences. For non-Microsoft
applications, you should consult the accompanying license agreement or contact
the licensor to determine whether application sharing is permitted by the
licensor.
* Support Services. Microsoft may provide you
with support services related to the SOFTWARE PRODUCT ("Support
Services"). Use of Support Services is governed by the Microsoft policies
and programs described in the user manual, in "online" documentation,
and/or in other Microsoft-provided materials.
Any supplemental software code provided to you as part of the Support Services
shall be considered part of the SOFTWARE PRODUCT and subject to the terms and
conditions of this EULA. With respect to technical information you provide to Microsoft
as part of the Support Services, Microsoft may use such information for its
business
purposes, including for product support and
development. Microsoft will not utilize such technical information in a form
that personally identifies you.
* Software Transfer. The initial licensee of
the SOFTWARE PRODUCT may make a one-time permanent transfer of this EULA and
SOFTWARE PRODUCT only directly to an end user. This transfer must include all
of the SOFTWARE PRODUCT (including all component parts, the media and printed
materials, any upgrades, this EULA, and, if applicable, the Certificate of
Authenticity). Such
transfer may not be by way of consignment or
any other indirect transfer. The transferee of such one-time transfer must
agree to comply with the terms of this EULA, including the obligation not to
further transfer this EULA and SOFTWARE PRODUCT.
* Termination. Without prejudice to any other
rights, Microsoft may terminate this
EULA if you fail to comply with the terms and conditions of this EULA. In such
event, you must destroy all copies of the SOFTWARE PRODUCT and all of its
component parts.
3. UPGRADES. If the SOFTWARE PRODUCT is
labeled as an upgrade, you must be properly licensed to use a product
identified by Microsoft as being eligible for the upgrade in order to use the
SOFTWARE PRODUCT. A SOFTWARE PRODUCT labeled as an upgrade replaces and/or
supplements (and may disable) the product that formed the basis for your
eligibility for the upgrade. You may use the resulting upgraded product only in
accordance with the terms of this EULA. If the SOFTWARE PRODUCT is
an upgrade of a component of a package of
software programs that you licensed as a single product, the SOFTWARE PRODUCT
may be used and transferred only as part of that single product package and may
not be separated for use on more than one COMPUTER.
4. COPYRIGHT. All title and copyrights in and
to the SOFTWARE PRODUCT (including but not limited to any images, photographs,
animations, video, audio, music, text, and "applets" incorporated
into the SOFTWARE PRODUCT), the accompanying printed materials, and any copies
of the SOFTWARE PRODUCT are owned by Microsoft or its suppliers. All title and
intellectual property
rights in and to the content that may be
accessed through use of the SOFTWARE PRODUCT is the property of the respective
content owner and may be protected by applicable copyright or other
intellectual property laws and treaties. This EULA grants you no rights to use
such content. If this SOFTWARE PRODUCT contains documentation that is provided
only in electronic form, you may print one copy of such electronic
documentation. You may not copy the
printed materials accompanying the SOFTWARE PRODUCT.
5. DUAL-MEDIA SOFTWARE. You may receive the
SOFTWARE PRODUCT in more than one medium. Regardless of the type
or size of medium you receive, you may use
only one medium that is appropriate for your single COMPUTER. You may not RUN
the other medium on another COMPUTER. You may not loan, rent, lease, or
otherwise transfer the other medium to another user, except as part of the
permanent transfer (as provided above) of the SOFTWARE PRODUCT.
6. BACKUP COPY. After installation of one copy
of the SOFTWARE PRODUCT pursuant to this EULA, you may keep the original media
on which the SOFTWARE PRODUCT was provided by Microsoft solely for backup or
archival purposes. If the original media is required to use the SOFTWARE
PRODUCT on the COMPUTER, you may make one copy of the SOFTWARE PRODUCT solely
for backup or archival purposes. Except as expressly provided in this EULA, you
may not otherwise make copies of the SOFTWARE
PRODUCT or the printed materials accompanying
the SOFTWARE PRODUCT.
7. U.S. GOVERNMENT RESTRICTED RIGHTS. All
SOFTWARE PRODUCT provided to the U.S. Government pursuant to solicitations
issued on or after December 1, 1995 is provided with the commercial rights and
restrictions described elsewhere herein. All SOFTWARE PRODUCT provided to the
U.S. Government pursuant to solicitations issued prior to December 1, 1995 is
provided with RESTRICTED RIGHTS as provided
for in FAR, 48 CFR 52.227-14 (JUNE 1987) or FAR, 48 CFR 252.227-7013 (OCT
1988), as applicable.
8. EXPORT RESTRICTIONS. This SOFTWARE PRODUCT
has been classified by the US Government as exportable under License Exception
TSU. Therefore the following terms apply: You agree that you will not export or
re-export the SOFTWARE PRODUCT, any part thereof, or any process or service
that is the direct product of the SOFTWARE PRODUCT (the foregoing collectively
referred to as the "Restricted Components"), to any country, person
or entity subject to U.S. export restrictions. You specifically agree not to
export or re-export any of the Restricted Components (i) to any country to
which the U.S. has embargoed or restricted the export of goods or services,
which currently include, but are not necessarily limited to Cuba, Iran, Iraq,
Libya, North Korea, Sudan and Syria, or to any national of any such country,
wherever located, who intends to transmit or transport the Restricted
Components back to such country; (ii) to any person or entity who you know or
have reason to know will utilize the Restricted Components in the design,
development or production of nuclear, chemical or biological weapons; or (iii)
to any person or entity who has been prohibited from
participating in U.S. export transactions by
any federal agency of the U.S. government. You warrant and represent that
neither the BXA nor any other U.S. federal agency has suspended, revoked or
denied your export privileges.
9. NOTE ON JAVA SUPPORT. THE SOFTWARE PRODUCT
MAY CONTAIN SUPPORT FOR PROGRAMS WRITTEN IN JAVA. JAVA TECHNOLOGY IS NOT FAULT
TOLERANT AND IS NOT DESIGNED, MANUFACTURED, OR INTENDED FOR USE OR RESALE AS
ON-LINE CONTROL EQUIPMENT IN HAZARDOUS ENVIRONMENTS REQUIRING FAIL-SAFE PERFORMANCE,
SUCH AS IN THE OPERATION OF NUCLEAR FACILITIES, AIRCRAFT NAVIGATION OR
COMMUNICATION SYSTEMS, AIR TRAFFIC CONTROL, DIRECT LIFE SUPPORT MACHINES, OR
WEAPONS SYSTEMS, IN WHICH THE FAILURE OF JAVA TECHNOLOGY COULD LEAD DIRECTLY TO
DEATH, PERSONAL INJURY, OR SEVERE PHYSICAL OR ENVIRONMENTAL DAMAGE.
MISCELLANEOUS
If you acquired this SOFTWARE PRODUCT in the
United States, this EULA is governed by the laws of the State of Washington.
If you acquired this SOFTWARE PRODUCT in
Canada, unless expressly prohibited by local law, this EULA is governed by the
laws in force in the Province of Ontario, Canada; and, in respect of any
dispute which may arise hereunder, you consent to the jurisdiction of the
federal and provincial courts sitting in Toronto, Ontario. If this SOFTWARE
PRODUCT was acquired outside the United States, then local law may apply.
Should you have any questions concerning this
EULA, or if you desire to contact Microsoft for any reason, please contact the
Microsoft subsidiary serving your country, or write: Microsoft Sales
Information Center/One Microsoft Way/Redmond, WA 98052-6399.
LIMITED WARRANTY
LIMITED WARRANTY FOR SOFTWARE PRODUCTS
ACQUIRED OUTSIDE THE U.S. AND CANADA. FOR THE LIMITED
WARRANTIES AND SPECIAL PROVISIONS PERTAINING TO
YOUR PARTICULAR JURISDICTION, PLEASE REFER TO YOUR
WARRANTY BOOKLET INCLUDED WITH THIS PACKAGE OR
PROVIDED WITH THE SOFTWARE PRODUCT PRINTED
MATERIALS.
LIMITED WARRANTY FOR SOFTWARE PRODUCTS
ACQUIRED IN THE U.S. AND CANADA. Microsoft warrants that (a) the
SOFTWARE PRODUCT will perform substantially in
accordance with the accompanying written materials for a period of ninety (90)
days from the date of receipt, and (b) any Support Services provided by
Microsoft shall be substantially as described in applicable
written materials provided to you by
Microsoft, and Microsoft support engineers will make commercially reasonable
efforts to solve any problem issues. Some states and jurisdictions do not allow
limitations on duration of an implied warranty, so the above limitation may not
apply to you. To the extent allowed by applicable law, implied warranties on
the SOFTWARE PRODUCT, if any, are limited to ninety (90) days.
CUSTOMER REMEDIES. Microsoft’s and its
suppliers’ entire liability and your exclusive remedy shall be, at Microsoft’s
option, either (a) return of the price paid, if any, or (b) repair or
replacement of the SOFTWARE PRODUCT that does not meet Microsoft’s Limited
Warranty and which is returned to Microsoft with a copy of your receipt. This Limited
Warranty is void if failure of the
SOFTWARE PRODUCT has resulted from accident,
abuse, or misapplication. Any replacement SOFTWARE PRODUCT will
be warranted for the remainder of the original
warranty period or thirty (30) days, whichever is longer. Outside the United
States, neither these remedies nor any product support services offered by
Microsoft are available without proof of purchase from an authorized
international source.
NO OTHER WARRANTIES. TO THE MAXIMUM EXTENT
PERMITTED BY APPLICABLE LAW, MICROSOFT AND ITS
SUPPLIERS DISCLAIM ALL OTHER WARRANTIES AND
CONDITIONS, EITHER EXPRESS OR IMPLIED, INCLUDING,
BUT NOT LIMITED TO, IMPLIED WARRANTIES OF
MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE,
TITLE, AND NON-INFRINGEMENT, WITH REGARD TO
THE SOFTWARE PRODUCT, AND THE PROVISION OF OR FAILURE
TO PROVIDE SUPPORT SERVICES. THIS LIMITED
WARRANTY GIVES YOU SPECIFIC LEGAL RIGHTS. YOU MAY HAVE
OTHERS, WHICH VARY FROM STATE/JURISDICTION TO
STATE/JURISDICTION.
LIMITATION OF LIABILITY. To the maximum extent
permitted by applicable law, in no event shall Microsoft or its
suppliers be liable for any special,
incidental, indirect, or consequential damages whatsoever (including, without
limitation, damages for loss of business profits, business interruption, loss
of business information, or any other pecuniary loss) arising out of the use of
or inability to use the SOFTWARE PRODUCT or the provision of or failure to
provide Support Services, even if Microsoft has been
advised of the possibility of such damages. In
any case, Microsoft’s entire liability under any provision of this EULA shall
be limited to the greater of the amount actually paid by you for the SOFTWARE
PRODUCT or U.S.$5.00; provided, however, if you have entered into a Microsoft
Support Services Agreement, Microsoft’s entire liability regarding Support
Services shall be governed by the terms of that agreement. Because some states
and jurisdictions do not allow the exclusion or limitation of liability, the
above imitation may not apply to you.
Unless you are an extremely strange member of our human race, it is unlikely that you read this EULA carefully or in its entirety. It is unlikely that the average user reads a EULA in its entirety despite the admonition to - READ CAREFULLY: at the beginning. Yet, if you or your company violates the terms of the EULA and you are brought to account for this violation the grief that can be precipitated upon you will certainly make you wish you had not committed the violation.
Even those who conscientiously desire to fully comply with a EULA can easily find them to be a headache. William Brandel says, “Tracking software licensing from a single-vendor source can be a headache. But trying to comply with software agreements can get downright complicated for managers who must manage licenses from multiple sources and at the same time administer a group of users who work with different applications at different times.” [Brandel94] Fortunately some steps are being taken to ease this burden. One such step is a new anti-piracy software audit tool offered by the Business Software Alliance. However, more can and should be done.
A Workable Solution Through Superior Architecture
Superior computer architecture can and should take steps to make
the software piracy problem obsolete forevermore. A Piracy Deterrent Bar is the
missing link that can make this possible.
·PDB
required should become a ubiquitous line on the system requirements
list. A Piracy Deterrent
Bar would have a visible part like a CD-ROM drive, a floppy drive, a
keyboard, a monitor, an external modem, a set of speakers, or the mouse. The visible part provides a matrix of easily
accessible sockets that can receive a specially coded ROM chip for each authorized
software product. The PDB could be
designed to attach to the parallel or serial port, but this should be an
important enough new item that, like the video monitor, it should rate its own
specially designed port and plug in card.
With its own special port and plug in card the PDB has the potential to
solve other existing dilemmas plaguing computer technology; notably the
CISC/RISC compatibility problem and Internet security.
The visible part of the PDB
would soon become as acceptable and expected as a CD-Rom Drive or monitor. The internal parts of the PDB would complete
the interface with the existing architecture.
In a nutshell the PDB would be most like an improvement of the hardware
lock with a few changes. Rather than
being able to only connect to a single parallel port, the PDB would offer a
matrix of sockets that special ROM chips matched with the protected software
product could be inserted into. The
socket matrix would solve the problem of no convenient way to stack all the
hardware locks out the back of the computer off of the parallel port. Computers that need to be upgraded would
require a PDB card to be installed and the actual bar that contains the bank of
sockets to be connected. A single bar
would have a finite number of sockets that could accommodate a typical number
of software applications found on most computer systems. Sometimes this typical number will be
exceeded, so a key feature of the PDB would be the ability to infinitely stack
bars by offering an additional port on each bar that another bar could attach to. This crucial feature would be similar to the
stackable hub concept of networks.
Chip technology has improved
dramatically since they were first created.
The price of the average chip has dropped substantially. In addition to burning all the necessary
CD’s when a software publisher is ready to offer a new product, the publisher
would order the necessary number of chips to go with each individual software
product. The software product with out
the accompanying chip would only be a demo version, or the number of times the
software could be used without the chip would be restricted or date
limited. Products downloaded from the
Internet could have a limited number of uses available that would provide
enough time for the chip to be delivered.
When the chip is inserted into a PDB, the software would be fully
functional. For cheaper software, all
the chips for a particular product could be identical so that as long as any
chip for the product was available, the product would be fully functional. For more expensive software, an individual
chip could be coded to match only an individual product. A chip could also contain information
indicating if the product was an upgrade and establish whether or not the other
components were present. Upgrades could
require that the previous chips were present so that the previous products
could not be used elsewhere. A user
could be free to load and leave his software wherever he wanted. However, when he left his friend’s PC he would
have to retrieve his chip if he wanted or needed a fully functional version
elsewhere. This would make software
more like a book than ever, except better.
The friend would have a demo version that he could fully evaluate to
make an informed purchase decision.
This could be a great marketing tool for software publishers providing a
win-win situation for users and venders alike.
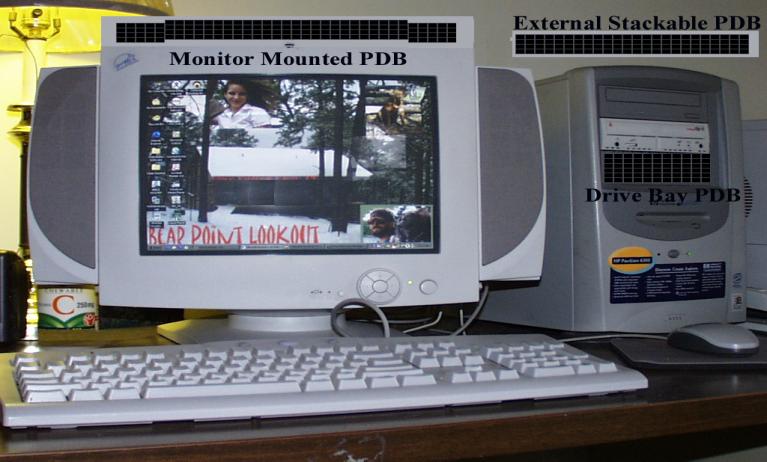
CD cases could be made with a
convenient niche to safely hold a chip during transport. New computers would soon have fashionable Piracy
Deterrent Bars as an integral part of the system unit case or the
monitor. Drive bay models could be
standard. When necessary, an external
stackable PDB would be available for upgrades on pre-generation machines and
for expansion on machines with an extremely large software inventory.
Typical Implementations Visible to
Users
Besides activating a software
product as fully functional when its chip is present the PDB could also perform
an inventory service and generate reports detailing which software is
available, the location of the chip and related chips in the matrix, and the
chip status, i.e. upgrade, standard version, professional version, premium
version, or academic version. How often
does software get installed and forgotten about now? The PDB would be a convenient source for keeping the user aware
of which software resources are available.
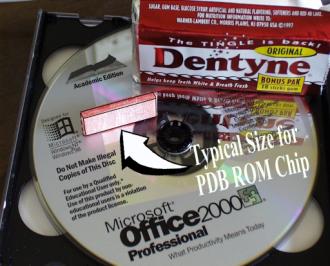
An ideal size for the PDB ROM Chip would be approximately the same as a stick of Dentyne chewing gum. This would allow a satisfactory number of chips to fit into a relatively small area while keeping them large enough to handle easily. The connectors would be on the end inserted into the socket while the other end should be designed to facilitate extraction when necessary.
Internet
Security with Positive User Identification When Necessary
A PDB can provide the
necessary logistics for additional features.
A major issue of keen interest today is Internet security. The PDB could supply a convenient location
for a user to insert a personal identification chip into the current computer
in use. These chips, properly packaged,
could be worn as Chip jewelry until needed.
For increased security, the chips could be used in combination with a
fingerprint reader, an iris scanner, or a facial recognition system that would
authenticate that the chip does indeed belong to the user. When a match is made with the on chip data
and the user’s personal feature of identity clearance would then be provided
for access to sites requiring the protection. No longer would an Internet site have to allow a stranger
inside unless they wanted too.
Transition
Mechanism from CISC TO RISC
CISC is a moribund
technology. RISC technology is far
superior to CISC. In his book, The
Microprocessor: A Biography, Michael Malone states that “Practically
speaking, eventually when RISC architectures reach the point when they can
duplicate (“emulate”) the CISC instruction set at about the same speed as CISC
machines, while still executing their own instruction set faster than CISC,
then the RISC approach will begin to dominate the PC market. When will that occur? Probably about the
turn of the century. Until then, total
sales tell the story ¾ and CISC machines, thanks to their compatibility and
strong software support, dominate the business.” [Malone95] The major problem here is that the large number of
software products that currently run on CISC machines need to continue to be
supported. This has been a mainstay of
the CISC success. Rather than RISC
attempting to simulate the CISC instruction set, with the Piracy Deterrent
Bar system a directing post can be maintained inside the computer. The PDB system can be designed to know what
resources are available inside a computer.
With the technology available today, there is no reason why a computer
cannot contain more than one architecture separate from each other yet
connected by the directing post. The
PDB ROM chip can contain information as to what systems the software is
compiled for. Multiple compilations can
be provided with each software package.
The directing post matches up the most efficient means of running the
software given what is available. If a
RISC compilation is available and the RISC architecture is available, the
directing post instantiates the RISC version.
If antiquated software does not have a PDB ROM chip, the CISC
architecture would be defaulted to.
This method would eliminate the need for RISC to emulate CISC
architecture. Once in place CISC
improvements could terminate with all the effort aimed at improving the
superior RISC technology.
Piracy Deterrent Bar Implementation
The Piracy Deterrent Bar is an idea whose time is long overdue. The major players in the computing industry can demonstrate their resolve to eliminate software piracy by collectively rallying behind this method and insisting that it become a common part of the system requirements list. A set of standards should be agreed upon and worked out as soon as possible. When the PDB is an accepted element of the system requirements list we can all press on to better concerns. In his book, “Computers & Social Controversy” Tom Logsdon mentions the Tiger Teams at ZARF and how they quickly breached the “multics” system designed by Honeywell Information Systems. The designers were confident that no one could breach its security. [Logsdon80] It would be naive to think that the Piracy Deterrent Bar could not be breached. Chip counterfeiting is a possibility among other things. However the Piracy Deterrent Bar is a marked improvement over the status quo for piracy prevention. The Tiger Teams at ZARF and their counterparts should be called on to play the “devil’s advocate” and ferret out any weak features that may exist with the Piracy Deterrent Bar so that they may be resolved. For the industry to neglect to solve this problem when it is technologically within its means to solve can only cause disaffection among the ranks of the honest end users who do their best to abide by the EULAs they are burdened with. The Piracy Deterrent Bar offers worthwhile side benefits in addition to piracy prevention. It can surely eliminate casual piracy and the need to be anchored to a EULA. It has the potential to put a serious dent in professional piracy operations and can definitely up the ante on penalties for those caught engaging in software piracy of PDB protected software. Software piracy no longer has to be the substantial problem it is!
Bibliography
book
[Baker84] Baker, Richard H. Scuttle the Computer Pirates: Software Protection Schemes. Blue Ridge Summit, PA: Tab Books Inc., 1984
[Clapes93] Clapes, Anthony L. Softwars: The Legal Battles for Control of the Global Software Industry. Connecticut: Quorum Books, 1993.
[Davis85] Davis III, G. Software Protection: Practical and Legal Steps to Protect and Market Computer Programs. New York: Van Nostrand Reinhold Company, 1985
[Freedman 99] Freedman, Alan The Computer Desktop Encyclopedia. New York: AMACOM, 1999.
[Logsdon80] Logsdon, Tom Computers & Social Controversy. Rockville, Maryland: Computer Science Press, 1980
[Malone95] Malone, Michael S. The Microprocessor: A Biography. Santa Clara, CA: TELOS, The Electronic Library of Science, 1995
internet
[BSA]Business Software Alliance, Employer Beware. http://www.bsa.org
[Brandel94] Brandel, William Computerworld 04-18-1994 New technology may ease licensing headache. Record(Bergen County), Electric Library
phone
[Straley] Straley, Mark Rainbow Technologies Inc. Rainbow Technologies Inc., 50 Technology Drive
Irvine, California 92618 Ph.(949)-450-7300