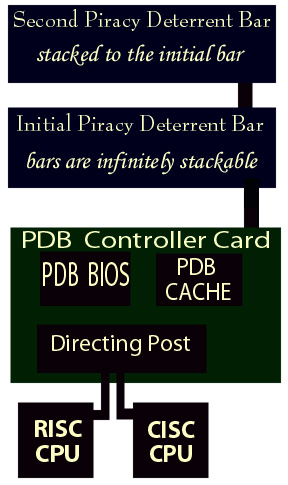
Piracy Deterrent Bar Implementation
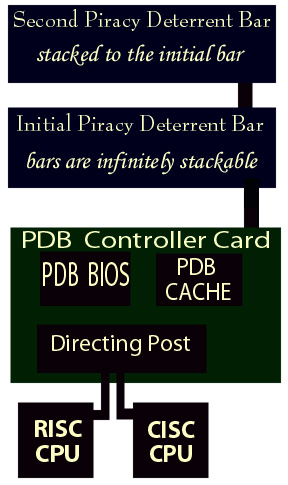
•During start up the Power On Self Test
causes the PDB BIOS to inventory the Piracy Deterrent Bar contents.
•The location in the matrix of any applications with a PDB ROM chip present
is mapped to the PDB Cache.
•The Directing Post evaluates the architecture and sets bits indicating
the availability or non-availability of specific types.
• When a PDB ROM chip is added or removed while the computer is running
an interrupt causes the inventory program to update the PDB Cache.
• When an application is requested for use the PDB Cache is interrogated.
(1) If a hit occurs, the PDB ROM chip that accompanies the application is accessed.
(2) Available compilations are determined and matched with the available architectures
determined by the directing post.
(3) Based on the available compilations and available architectures an efficiency
hierarchy invokes the best compilation to run the program and the application
is directed to the appropriate architecture.
(4) If a PDB ROM chip is not present for a requested application then the CISC
architecture is defaulted to.
(5) Depending on the age and version of the application the user has access
to a fully functional application or a restricted demo version.